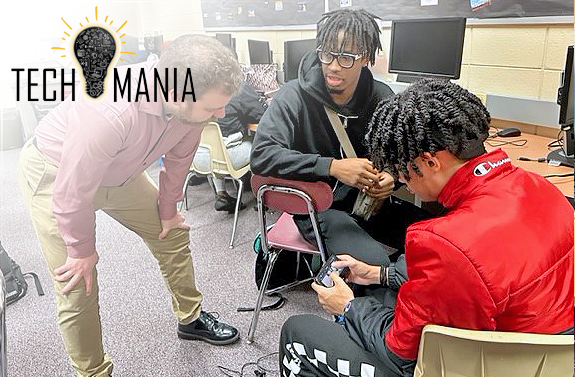
In the face of so many options these days, discovering cyber career pathways can be intimidating for most K-12 students. The FMA believes an effective means to support students developmentally is to expose them to what’s out there in the real world so that they can further discover their talents and interests.
Together with our FMA member companies, Tech Mania does just that.
FULL PHOTO GALLERY
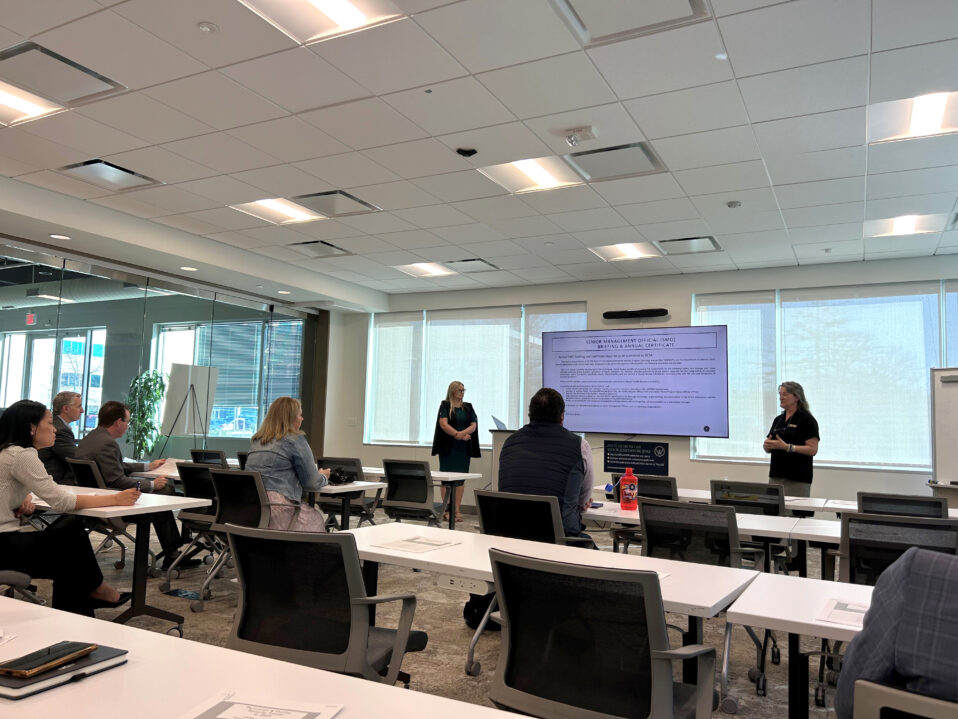
Kicked-off the last week in October and ending mid-December, FMA’s fall 2022 Tech Mania spans across seven weeks and seven schools in Howard and Anne Arundel County. Before the end of this year, six of our FMA member companies will have given 20 presentations to approximately 392 students, bolstering any interest in STEM-based careers. Topics included the latest technology utilized in construction projects, monitoring the health of the Chesapeake Bay, neural network structure, encryption, cybersecurity and even an autonomous Navy vessel.
Thank you to our participating schools from Howard and Anne Arundel County: Applications and Research Laboratory (ARL) Early Cybersecurity, Glen Burnie High School, Hammond High School, Long Reach High School, Marriotts Ridge High School, SOUTH RIVER HIGH SCHOOL PTSO and Wilde Lake High School.
Special thanks to BigBear.ai, Leidos, Lockheed Martin, National Security Agency, National Security Agency with Learning Undefeated and The Whiting-Turner Contracting Company for helping students learn about modern technology directly from those creating it!
Presentation Topics
BigBear.ai
Introduction to Neural Networks
Presentation Objectives
- Describe the learning process of an artificial neural network (ANN).
- Identify different types of nodes in an ANN.
- Employ an ANN to classify data points into known labels.
Activity Format
Students will be given access to a Jupyter notebook with step-by-step instructions on how to modify the structure of a neural network. During this group activity, they will be able to try different approaches to improve the performance of the neural network. Students will be able to discuss any modifications they made to the architecture of the neural network, or any ideas they might have towards the improvement of the neural network.
Leidos
Resilient Design
Presentation Objectives
- Understand what a cyber-threat is, and how it impacts various types of targets.
- Understand the connectivity between systems in a modern world.
- Understand how design practices, in addition to cybersecurity, are needed to mitigate threats.
Activity Format
We will discuss the Leidos SeaHunter, an autonomous navy vessel. Sea Hunter is the first of a new class of warships that use artificial intelligence in place of a crew. Students will be asked to identify areas susceptible to a cyber threat, and potential mitigations. We will review the students thoughts from the small-group activity and highlight design features we, Leidos, are actually including in our SeaHunter system.
Lockheed Martin
5 D’s of Hacking
Presentation Objectives
- Know the 5 D’s of cyber security.
- Be able to connect each D to their real life.
- In the end, they should be able to talk to their family and tell them about how they can stay safe online.
Activity Format
In small groups the class will be split up into the red team and blue. One team is defenders and one team is the attackers. Students pick what they would like to hack or defend and come up with ways to either hack or defend that particular system going through the 5 D’s of Cybersecurity.
National Security Agency (NSA)
Cryptanalysis 101
Presentation Objectives
Students will learn basic cryptology terminology and four classic encryption techniques plus the mathematics behind the cryptanalysis (frequency counts and cipher patterns). Students will decrypt several messages using substitution and transposition techniques.
Northrop Grumman and Learning Undefeated
Chesapeake Bay Oyster Monitoring Grand Challenge
Presentation Objectives
- Students will know what the Chesapeake Bay Oyster Monitoring Grand Challenge is and how Northrop Grumman’s partnership is helping to protect the oysters in the Chesapeake Bay.
- Students will be able to analyze and interpret real world data.
- Students will be able to make recommendations based on real-world data.
Activity Format
Students will break out into small groups to interpret real oyster monitoring data sets. While working with these data sets, students will need to come to a consensus about what the data is “saying”. They will then need to make a recommendation on next set of actions based off the data they have been given. Student groups will then share out by stating their interpretation of the data and how that interpretation informed their recommendation for next steps.
Whiting Turner
Virtual Design and Construction (VDC) Utilization
Presentation Objectives
- Understand the general use of VDC and technology in construction.
- Recognize the opportunity and career path of VDC in construction.
- Understand the importance of problem solving.
Activity Format
Activity will be a web-hosted scavenger hunt created in Kuula 360 software. WT uses this platform to create tours for our team and clients. The scavenger hunt will include multiple 360 images with icons indicating potential safety of constructability concerns for students to identify. Students will race to find all issues through each location in a scavenger hunt format. Students will be able to scan a QR code to review this tour via their phone or laptop. They can additionally follow along with others or the presenters. WT will review how our team uses this model to search for issues in coordination, similar to a scavenger hunt in itself, to find and resolve problems.